Meet
Prasanth.
I'm a fresher Azure Cloud Engineer based in Bengaluru, specializing in cloud security, monitoring, and governance. I hold a Post Graduate Diploma in Cloud Data Management from Conestoga College, Canada.
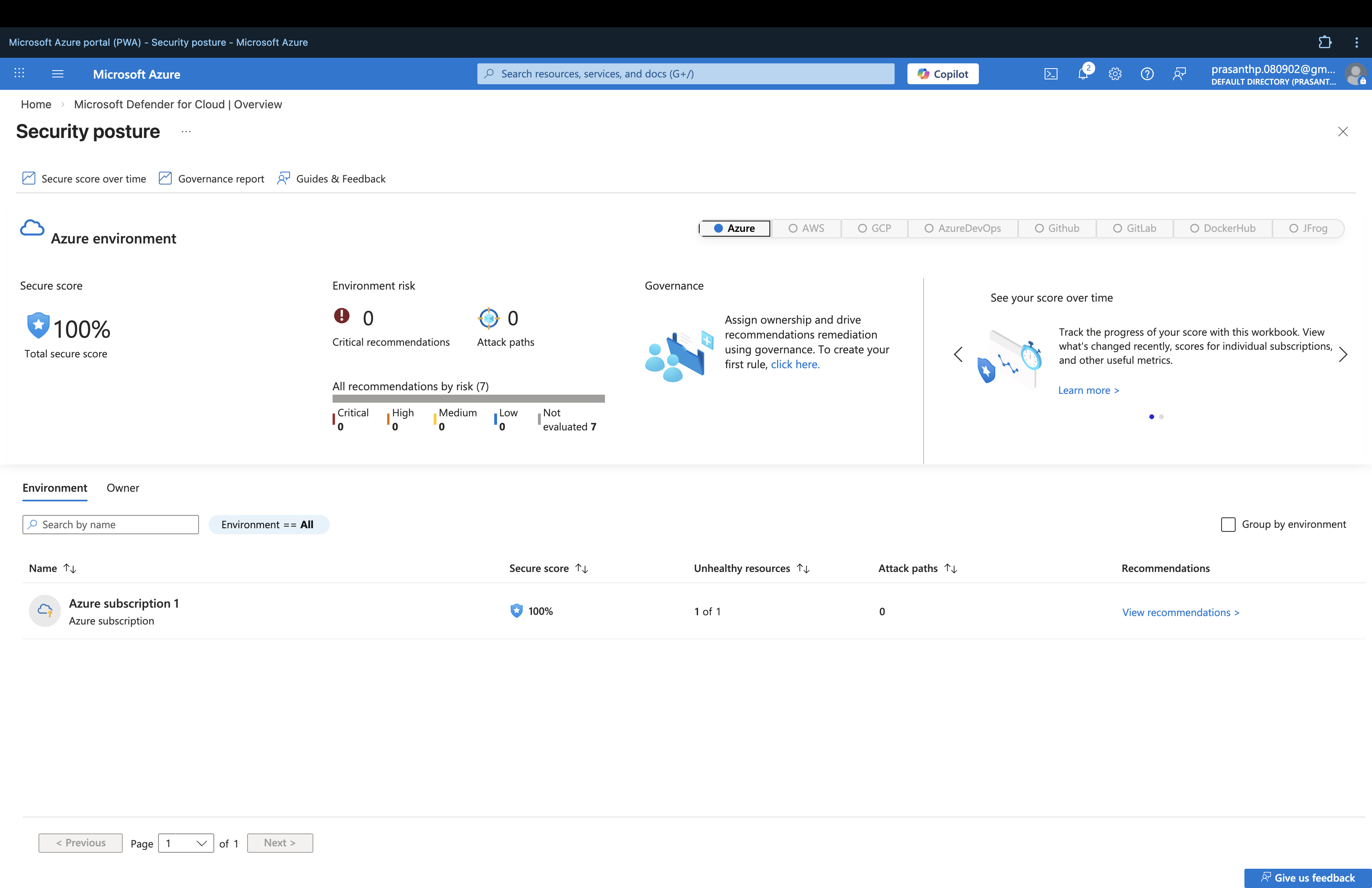
I've built two enterprise Azure projects — CloudGuard (6-phase secure cloud infrastructure covering VNet, NSG, RBAC, KQL monitoring, Azure Policy, and Defender for Cloud) and CloudGuard IaC Pipeline (Terraform + GitHub Actions CI/CD automating full Azure infrastructure deployment).